Security
For any new or existing WordPress website, you should ensure that you have some sort of software firewall installed. A plugin that will report on suspicious activity and files within your WordPress file system. We recommend WordFence. Even having the basic version of WordFence will help tremendously.
In regards to file and folder permissions, files should have permissions set to 644 and folders 755. Using a FTP/SFTP program, such as FileZilla, you can easily update all files and/or folders in just a few clicks.
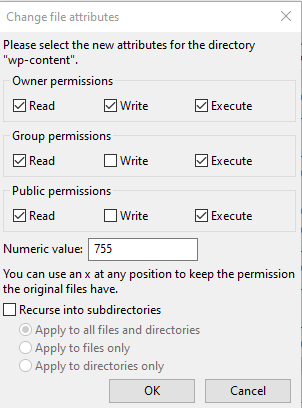
We do not recommend right-clicking your public_html folder and doing this, as it may change the permissions on public_html, which is usually set to 750. Instead, you may want to highlight/select all files and folders in your WordPress directory. Once you have your files/folders selected, right-click one and click File Permissions. At the bottom of the window (see above), check Recurse into subdirectories, then select either Apply to files only or Apply to directories only. Depending on which you choose to do first, type in 644 for files or 755 for directories in the Numeric value: field. It will take a few minutes for each update to run.
My Website Has Been Hacked!
If you can access the admin panel of your site and view the scan logs from WordFence, or other protection plugin, then you should have a list of files that were found to be malicious. If not, that’s OK. You can still perform the following steps.
You will want to login to access your website’s files, using a program like FileZilla or your web host’s File Manager. Look for any files that were listed in the scan, or any files/folders with incorrect permissions. With each file found, you will want to do 2 things:
- Fix the permissions on the file/folder. Also make sure the folder that contains this item has proper permissions.
- Using a fresh copy of WordPress, upload and replace the file. You can find out your version of WordPress by opening /wp-includes/version.php. You can download the matching version of WordPress from: https://wordpress.org/download/releases/
Once you patch all the malicious files, you will want to run another scan. Again, WordFence is great for this; and is the very first plugin we install on a website. If you do decide to use WordFence, you will be prompted to enter your email address, and if you decide to opt-in you will receive notices about outdated plugins and any issues that arise.
Side Note
Hackers don’t usually have the time to manually attack a website, unless it’s a personal vendetta. Instead, they send out a bot which looks for sites with vulnerabilities. The hacker’s code is then automatically uploaded and executed. Knowing this, the typical flaw in websites that allows attackers to get in are the file permissions. However, there are many other ways an attacker may gain access to your site. Some of the ways include: cross-site scripting (due to how some plugins may be written), and allowing unauthenticated users to upload files. Uploads should be limited to specific file types, and all users who are allowed to upload files should be authenticated first.
Keep Your WordPress Site Updated
It is very important to keep WordPress, plugins and themes updated. In some cases it may not be realistic to update certain things right away, but in that case make sure you take a quick glace at what the new release includes, as it may be patching an exploit.
When you setup and configure wp-config.php, don’t forget to generate and apply the your Unique Keys and Salts, found below your DB_* definitions.
Also make sure you use strong passwords, with uppercase, lowercase, numbers and special characters, having a length no less than 11.
If You Need Help With Your Hacked Site
Feel free to give us a call. We have fixed many hacked websites in our 25+ years of service, and the underlying exploit is almost always the same. It usually takes less than 2 hours to fix a website. In some cases, your website can be restored from a backup. However, if you restore from a backup, we recommend glancing over the files and folders to ensure the correct permissions have been set.






